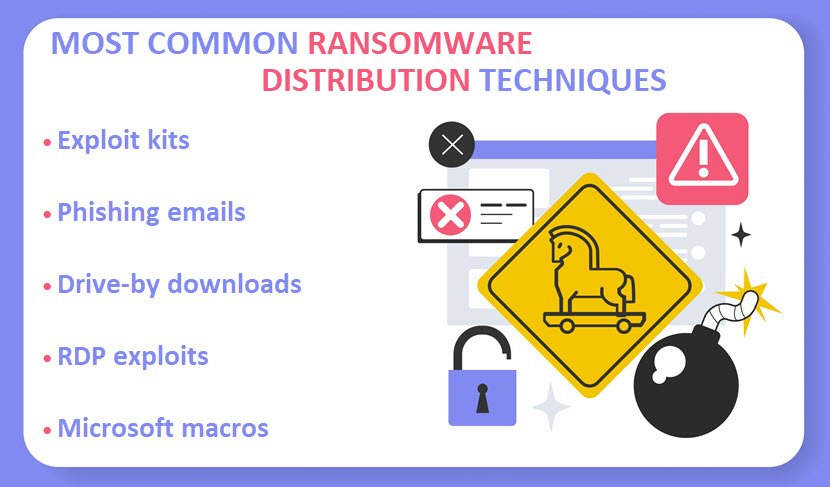
Different There While there are many ways to infect a device, most cybercriminals rely on several tried-and-tested methods of ransomware delivery.
Knowing these usual distribution techniques and how an average cybercriminal thinks is vital to your ability to block infection attempts.
This article presents five go-to strategies criminals use to deliver ransomware to target devices
. Jump in to learn about the most common infection methods and see whether your ransomware detection and prevention strategies require updating.Check out pNAP’s ransomware protection page and see how we use a unique mix of immutable backups and cloud-based DR to protect our clients.
Most Common Ways Ransomware Is Delivered
So, how is ransomware delivered? Below is an in-depth look at the most common and most effective ransomware distribution techniques.
Exploit Kits
An exploit kit is a prepackaged bundle of tools criminals use to deliver various types of malware to vulnerable systems. Kits automate the process of finding and exploiting known flaws in software and web browsers.
Here’s how an exploit kit typically deploys ransomware:
A device gets infected with an exploit kit, e.g., via a malicious ad or by visiting an infected website.
- A kit scans the victim’s system to identify specific software flaws.
- If the kit detects a fitting vulnerability, it uses a set of weaponized exploits that specifically target the found flaw.
- An exploit delivers the ransomware payload to the victim’s system. Kit ).
- The payload encrypts the user’s files and displays a ransom note.
- Criminal groups maintain exploit kits the same way legit companies manage software products. Each kit has a lifecycle during which designers remove outdated and add new exploits.
How to Defend Against Exploit Kits
Here are the most effective ways to counter the threat of exploit kits armed with ransomware payloads:
Regularly apply the latest patches to all software on your systems.
- Use antivirus and anti-malware software with the latest updates.
- Deploy advanced threat protection that detects and blocks exploit kit activity.
- Use application whitelisting to ensure only authorized and trusted software runs on the system.
- Have as few browser plugins as possible (and delete any you don’t use regularly).
- Boost network security by monitoring traffic for signs of exploit kit activity and analyzing logs to identify potential threats.
- Educate employees on how exploit kits work and ensure everyone understands the risks of suspicious websites and unexpected pop-ups.
- Exploit kits are often available for purchase or rent on the Dark Web. That way, even less tech-savvy criminals get to launch advanced attacks without having to develop their own exploits.
Email Phishing
Ransomware phishing occurs when a criminal uses a legitimate-looking or a hacked email address to send a message to trick the victim into one of the two:
Clicking a malicious URL that redirects the target to a site that triggers the download of malware.
- Opening an attachment that, once clicked or interacted with, delivers a malware payload.
- Phishing emails are
the cause of an estimated two-thirds of all ransomware infections. Criminals use two distinct phishing tactics to deliver ransomware:Spray-and-pray campaigns that send out infected emails to random targets.
- More precise spear-phishing in which a criminal sends a personalized email to each target.
- Phishing tactics typically appeal to human greed or fear, so the most common strategies include:
Offering money, discounts, or prizes.
- Sending fake invoices.
- Informing the target that their checking or PayPal account is frozen or hacked.
- Sending urgent requests to low-ranking employees. 01 The attacker copies a legitimate email that the victim received earlier, changes the attachment or link in the message to a malicious one, and “resends” the message.
- How to Defend Against Email Phishing
Phishing attacks work because they exploit human errors and the lack of awareness. Stopping phishing attempts requires high levels of email security and ensuring all potential targets follow good cybersecurity practices, such as:Always verify the sender’s email address to ensure it matches the official domain of the company they claim to represent.Hover over links to see the actual URL before clicking.
Be cautious of unexpected attachments from unknown sources.
Avoid providing sensitive info in response to email requests.
- When in doubt, contact the sender or their organization directly on the phone or in person.
- Organize security awareness training to improve your workforce’s readiness for cyber attacks and boost phishing awareness among your employees.
- Drive-By Downloads
- A drive-by download happens when a victim visits a compromised or malicious website that automatically and stealthily delivers malware to the user’s device.
- Unlike other ransomware distribution techniques that require direct user interaction (e.g., clicking a malicious link or opening an infected attachment), a drive-by download only requires the victim to visit the infected website.
Criminals set up drive-by downloads in several different ways, including the following methods:

Compromising legitimate websites with vulnerabilities in their backend.
Creating new malicious websites for the sole purpose of performing drive-by downloads.
Exploiting vulnerabilities in web browsers or their plugins (typically Adobe Flash or Java).
Setting up malicious ads that pop up on legitimate websites.
- Using redirects or iframe injections to get the victim to a malicious website.
- When the victim visits an infected website, the drive-by download occurs automatically. Malicious code enters the system and executes without any warning or indication of what’s happening.
- How to Defend Against Drive-By Downloads
- Here’s how to protect yourself and your workforce from drive-by downloads:
- Keep browsers, plugins, and OSes up to date with the latest security patches.
Delete unnecessary browser plugins.
Enable built-in security features of your browser (e.g., pop-up blockers, anti-phishing filters, safe browsing settings, etc. ).
Set up a Web Application Firewall (WAF), a type of firewall that blocks malicious web traffic and prevents access to compromised websites.
- Implement a content security policy (CSP) to prevent the execution of unauthorized scripts on web pages.
- Configure browsers to enable click-to-play for plugins such as Adobe Flash and Java. That way, you ensure plugins only run when explicitly allowed by the user.
- Use antivirus and anti-malware software to detect and block malicious downloads.
- Boosting overall endpoint security is another effective way to protect your workforce from drive-by download attempts.
- RDP Exploits
- Exploiting the Remote Desktop Protocol (RDP) is another common ransomware distribution technique. RDP is a Microsoft communications protocol that enables users to connect to and remotely control another computer over a network.
- Cybercriminals use an automated tool to scan the internet for systems with open RDP ports (
by default, RDP receives connection requests through port 3389
). Once they identify a potential victim, criminals attempt to gain access to the target system.
Brute-force attacks and credential stuffing are standard techniques for gaining unauthorized access. Criminal Once The ransomware encrypts files on the system and, in some cases, spreads laterally across the network to infect other devices.
How to Defend Against RDP ExploitsPreventing criminals from using RDP to deliver ransomware requires the following precautions:Always change the default RDP port.
Keep the operating system and RDP software up to date with the latest patches to avoid zero-day exploits.
Implement robust monitoring to detect and block suspicious RDP login attempts.
Restrict RDP access to specific IP addresses.
Implement two-factor authentication (2FA) for all remote desktop sessions.
- Set up account lockouts to prevent brute-force attacks.
- Enforce the use of unique and strong passwords for RDP accounts.
- Use our free password generator to create secure credentials immune to brute-force attacks.
- Microsoft Macros
- Microsoft macros are small programs or scripts that automate tasks within Office apps (Word, Excel, PowerPoint, Outlook, etc.). While macros are helpful to users, criminals often use macros to deliver malicious payloads.
- Criminals create an Office file (typically either an Excel or Word file) and include a malicious macro. Then, they use social engineering to trick users into opening the file and activating the macro.
- If the user activates the macro in the infected file, the embedded code executes, and the macro either:
Downloads ransomware payload from a remote server.
Executes the ransomware code already present within the document.
Once ransomware executes, malicious code begins encrypting target files on the system, and the victim gets a note demanding a ransom in exchange for the decryption key.
How to Defend Against Microsoft Macros
Here are a few precautions that lower the risk of suffering ransomware via a file containing an infected macro:
- Enable macro security warnings in Microsoft Word.
- Never ignore warnings that pop up when a document contains macros.
Leave macros disabled if you do not require them for daily tasks (which is the default Microsoft setting). Only enable macros when you need them and when the document arrives from a trusted source.
Use email filters to block suspicious documents.
Keep Microsoft Office software up to date with the latest security patches.
- Educate employees about the risks of enabling macros and the importance of being cautious when working with suspicious documents.
- Want to learn more about ransomware? Check out the following articles:
- Most Common Ransomware Encrypted File Extensions
- When ransomware encrypts data, malicious code changes the file extension. The The table below presents an extensive list of the most common file extensions that indicate a ransomware infection.
- Important note:
- Ransomware criminals are not known for politeness or sophistication, so the table below contains some highly graphic language.
Reader discretion is advised

.
Infected file extension
Ransomware variant._AiraCropEncryptedAiraCrop.1cbu1
| Princess Locker | .1txt |
|---|---|
| Enigma | .73i87A |
| Xorist | .a5zfn |
| Alma Locker | .aaa |
| TeslaCrypt | .abc |
| TeslaCrypt | .adk |
| Angry Duck | .aesir |
| Locky | .alcatraz |
| Alcatraz Locker | .angelamerkel |
| Angela Merkel | .AngleWare |
| HiddenTear/MafiaWare | .antihacker2017 |
| Xorist | .atlas |
| Atlas | .axx |
| AxCrypt encrypted data | .BarRax |
| BarRax (HiddenTear variant) | .bin |
| Alpha/Alfa | .bitstak |
| Bitstak | .braincrypt |
| Braincrypt | .breaking_bad |
| Files1147@gmail(. )com | .bript |
| BadEncriptor | .btc |
| Jigsaw | .ccc |
| TeslaCrypt or Cryptowall | .CCCRRRPPP |
| Unlock92 | .cerber |
| Cerber | .cerber2 |
| Cerber 2 | .cerber3 |
| Cerber 3 | .coded |
| Anubis | .comrade |
| Comrade | .conficker |
| Conficker | .coverton |
| Coverton | .crab |
| GandCrab | .crinf |
| DecryptorMax or CryptInfinite | .crjoker |
| CryptoJoker | .crptrgr |
| CryptoRoger | .cry |
| CryLocker | .cryeye |
| DoubleLocker | .cryp1 |
| CryptXXX | .crypt |
| Scatter | .crypte |
| Jigsaw | .crypted |
| Nemucod | .cryptolocker |
| CryptoLocker | .cryptowall |
| Cryptowall | .crypz |
| CryptXXX | .czvxce |
| Coverton | .d4nk |
| PyL33T | .dale |
| Chip | .damage |
| Damage | .darkness |
| Rakhni | .dCrypt |
| DummyLocker | .deadbolt |
| Deadbolt | .decrypt2017 |
| Globe 3 | .derp |
| Derp | .Dexter |
| Troldesh | .dharma |
| CrySiS | .dll |
| FSociety | .dxxd |
| DXXD | .ecc |
| Cryptolocker or TeslaCrypt | .edgel |
| EdgeLocker | .enc |
| TorrentLocker | .enciphered |
| Malware | .EnCiPhErEd |
| Xorist | .encr |
| FileLocker | .encrypt |
| Alpha | .encrypted |
| KeRanger OS X | .enigma |
| Coverton | .evillock |
| Evil-JS | .exotic |
| Exotic | .exx |
| Alpha Crypt encrypted file | .ezz |
| Alpha Crypt virus encrypted data | .fantom |
| Fantom | .file0locked |
| Evil | .fucked |
| Manifestus | .fun |
| Jigsaw | .gefickt |
| Jigsaw | .globe |
| Globe | .good |
| Scatter | .grt |
| Karmen HiddenTear | .ha3 |
| El-Polocker | .helpmeencedfiles |
| Samas/SamSam | .herbst |
| Herbst | .hnumkhotep |
| Globe 3 | .hush |
| Jigsaw | .ifuckedyou |
| SerbRansom | .info |
| PizzaCrypts | .kernel_complete |
| KeRanger OS X | .kernel_pid |
| KeRanger OS X | .kernel_time |
| KeRanger OS X | .keybtc@inbox_com |
| KeyBTC | .kimcilware |
| KimcilWare | .kkk |
| Jigsaw | .kostya |
| Kostya | .krab |
| GandCrab v4 | .kraken |
| Rakhni | .kratos |
| KratosCrypt | .kyra |
| Globe | .lcked |
| Jigsaw | .LeChiffre |
| LeChiffre | .legion |
| Legion | .lesli |
| CryptoMix | .lock93 |
| Lock93 | .locked |
| Various | .locklock |
| LockLock | .locky |
| Locky | .lol! |
| GPCode | .loli |
| LOLI RanSomeWare | .lovewindows |
| Globe | .madebyadam |
| Roga | .magic |
| Magic | .maya |
| HiddenTear | .MERRY |
| Merry X-Mas | .micro |
| TeslaCrypt 3.0 | .mole |
| CryptoMix | .MRCR1 |
| Merry X-Mas | .noproblemwedecfiles |
| Samas/SamSam | .nuclear55 |
| Nuke | .odcodc |
| ODCODC | .odin |
| Locky | .onion |
| Dharma | .oops |
| Marlboro | .osiris |
| Locky | .p5tkjw |
| Xorist | .padcrypt |
| PadCrypt | .paym |
| Jigsaw | .paymrss |
| Jigsaw | .payms |
| Jigsaw | .paymst |
| Jigsaw | .paymts |
| Jigsaw | .payrms |
| Jigsaw | .pays |
| Jigsaw | .pdcr |
| PadCrypt | .pec |
| PEC 2017 | .PEGS1 |
| Merry X-Mas | .perl |
| Bart | .PoAr2w |
| Xorist | .potato |
| Potato | .powerfulldecrypt |
| Samas/SamSam | .pubg |
| PUBG | .purge |
| Globe | .pzdc |
| Scatter | .r5a |
| 7ev3n | .raid10 |
| Globe | .RARE1 |
| Merry X-Mas | .razy |
| Razy | .rdm |
| Radamant | .realfs0ciety@sigaint.org.fs0ciety |
| Fsociety | .rekt |
| HiddenTear | .rekt |
| RektLocker | .remk |
| STOP | .rip |
| KillLocker | .RMCM1 |
| Merry X-Mas | .rmd |
| Zeta | .rnsmwr |
| Gremit | .rokku |
| Rokku | .rrk |
| Radamant v2 | .ruby |
| Ruby | .sage |
| Sage | .SecureCrypted |
| Apocalypse | .serp |
| Serpent | .serpent |
| Serpent | .sexy |
| PayDay s | .shit |
| Locky | .spora |
| Spora | .stn |
| Satan | .surprise |
| Surprise | .szf |
| SZFLocker | .theworldisyours |
| Samas/SamSam | .thor |
| Locky | .ttt |
| TeslaCrypt 3.0 | .unavailable |
| Al-Namrood | .vbransom |
| VBRansom 7 | .venusf |
| Venus Locker | .VforVendetta |
| Samsam | .vindows |
| Vindows Locker | .vvv |
| TeslaCrypt 3.0 | .vxlock |
| vxLock | .wallet |
| Globe 3 | .wcry |
| WannaCry | .wflx |
| WildFire | .Whereisyourfiles |
| Samas/SamSam | .windows10 |
| Shade | .wncry |
| Wana Decrypt0r 2.0 | .xxx |
| help_dcfile | .xyz |
| TeslaCrypt | .ytbl |
| Troldesh | .zcrypt |
| ZCRYPT | .zepto |
| Locky | .zorro |
| Zorro | .zyklon |
| ZYKLON | .zzz |
| TeslaCrypt | .zzzzz |
| Locky | If you ever fall victim to ransomware, use the table above to identify the variant that infected your data. Double At worst, knowing what variant entered your system will help authorities better instruct you on how to recover from the attack. |
| Stay a Step Ahead of Would-Be Cybercriminals | Like all criminals, ransomware groups prefer going after low-hanging fruit. Ran |
